Category: Tech

March 04, 2026
Tech
The Download: Earth’s rumblings, and AI for strikes on Iran
The must-reads I’ve combed the internet to find you today’s most fun/important/scary/fascinating stories about technology. 1 How Anthropic’s AI tool…

March 04, 2026
Tech
The Best Linux Laptops (I Install Linux on Every Laptop I Test) (2026)
Here’s a list of its ports: 1 × USB 4.0 Type-C, 1 × USB 3.2 Gen 2 Type-C, 3 ×…

March 04, 2026
Tech
I’m not ashamed to admit the Kobo Remote is the best gadget I’ve bought this year
Does anyone really need a remote for a device you’re already either holding or using at arm’s length? E-readers have…

March 04, 2026
Tech
Who needs data centers in space when they can float offshore?
The power crunch for AI data centers has gotten so severe that people — not just Elon Musk — are talking about…
March 04, 2026
Tech
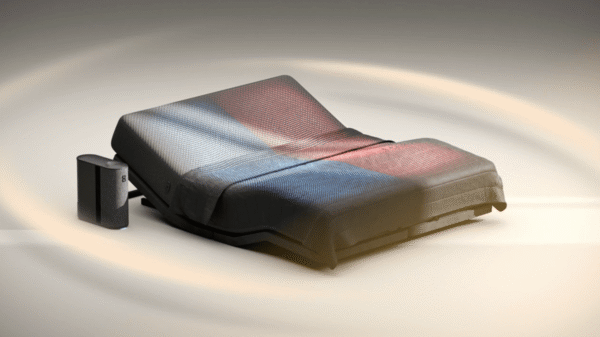
Eight Sleep raises $50M at $1.5B valuation
Sleep tech company Eight Sleep today said that it has raised $50 million in a strategic round led by Tether…

March 04, 2026
Tech
Best Theraguns and Therabody Tools for Smarter Recovery (2026)
Honorable Mentions Photograph: Boutayna Chokrane TheraFace Mask for $650: The TheraFace Mask is a cordless, hands-free light-therapy device that uses…

March 04, 2026
Tech
What It’s Like to Have a Brain Implant for 5 Years
Initially, Gorham used his brain-computer interface for single clicks, Oxley says. Then he moved on to multi-clicks and eventually sliding…

March 04, 2026
Tech
These Official ChromeOS Flex USB Sticks Can Give Your Old Mac or Windows PC a Second Life
“People want something that lasts them a long time, that is quality, that is useful,” says Google senior director Alexander…

March 04, 2026
Tech
TECNO’s Modular Magnetic Smartphone Concept Revives a Forgotten Dream
Smartphones have evolved into a rather predictable shape over time, with flat slabs, fixed cameras, and batteries well sealed up…

March 04, 2026
Tech
Leaked government-grade iPhone hacking tools now used to steal crypto and data from users
According to new technical analyses from Google and mobile security firm iVerify, Coruna’s technical core comprises five complete exploit chains…